Implement Virtual Networks
- By Dan Patrick, Rick Rainey, Steve Ross, Michael Washam
- 4/10/2018
- Skill 4.1: Configure Virtual Networks
- Skill 4.2: Design and implement multi-site or hybrid network connectivity
- Skill 4.3: Configure ARM VM Networking
- Skill 4.4: Design and implement a communication strategy
- Thought experiment
- Thought experiment answers
- Chapter summary
Skill 4.4: Design and implement a communication strategy
This section focuses on the various methods and connectivity choices to securely extend your on-premises network into the Microsoft cloud. There are two types of connections for connecting to the MS cloud covered in this section: the S2S VPN and an Azure resource known as Azure App Hybrid Connections for exposing services inside your network without a VPN.
Leverage Site-to-Site (S2S) VPN to connect to an on-premises infrastructure
S2S connections are used for building hybrid configurations. Once established between your VPN on-premises device and an Azure VPN Gateway, this connection type allows your on-premises users and VMs to VMs and services that are running in an Azure VNet.
Running workloads in the cloud and on-premises is very common and as such, these connections make this possible. In the case of adding a VPN connection to Azure you are essentially just adding another datacenter to your network; it just happens to be the public Azure cloud.
Figure 4-64 shows a VNET that has been connected to an on-premises datacenter by using ExpressRoute. There is an intranet SharePoint farm deployed along with its data tier and domain controllers. Notice the use of the multiple load balancers to facilitate the deployment requirement of the application. This entire Virtual Network, application, data, and identity is available and functional for the clients that are on the other side of the ExpressRoute circuit.
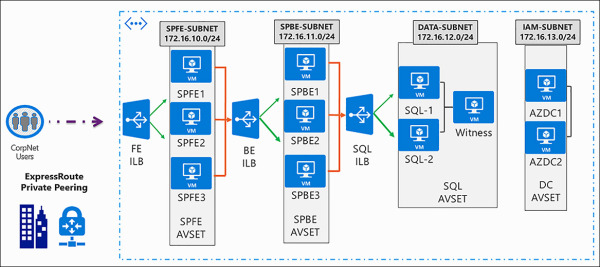
FIGURE 4-64 Virtual Network and Services connected to On-premises using ExpressRoute
Implement Hybrid Connections to access data sources on-premises
Within the Azure App Service, hybrid connections can be used to access application resources in other networks. This connection provides access FROM your application running in Azure TO an application endpoint hosted in your datacenter. It does this is such a way that there is not a requirement to build out a complex full S2S or hybrid cloud infrastructure.
In many scenarios, this type of connection solves the problem customers have if that want to build an application in the cloud, but the data is “locked,” in their datacenter. By using the hybrid connection in Azure, the App Service can connect to that data. Figure 4-65 shows a functional diagram of this type of hybrid connection.
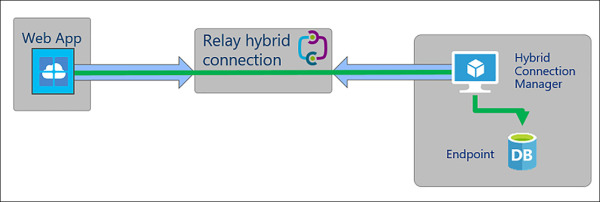
FIGURE 4-65 Hybrid Connection from App Services to an On-premises Database
When these connections are created it only allows the Web App to talk to the datacenter. It does not enable full communication between the local server and the Web App running in Azure. Each hybrid connection correlates to a single TCP host and port combination. This means that the hybrid connection endpoint can be on any operating system and any application, provided you are hitting a TCP listening port. Hybrid connections do not know or care what the application protocol is or what you are accessing. It is simply providing network access.
The hybrid connections feature consists of two outbound calls to Service Bus Relay. There is a connection from a library on the host where your app is running in the app service and then there is a connection from the Hybrid Connection Manager (HCM) to Service Bus Relay. The HCM is a relay service that you deploy within the network hosting.
Through the two joined connections your app has a TCP tunnel to a fixed host:port combination on the other side of the HCM. The connection uses TLS 1.2 for security and SAS keys for authentication/authorization.
There are many benefits to the hybrid connections capability including:
Apps can securely access on premises systems and services securely
The feature does not require an internet accessible endpoint
Each hybrid connection matches to a single host:port combination, which is an excellent security aspect
It normally does not require firewall holes as the connections are all outbound over standard web ports
The feature is running at the network level, so it is agnostic to the language used by your app and the technology used by the endpoint
