Autoruns
- By Aaron Margosis and Mark Russinovich
- 2/17/2017
- Autoruns fundamentals
- Autostart categories
- Saving and comparing results
- AutorunsC
- Autoruns and malware
Autostart categories
When you launch Autoruns for the first time, all autostart entries on the system are displayed in one long list on the Everything tab. As Figure 4-8 shows, the display includes up to 19 other tabs that break down the complete list into categories.
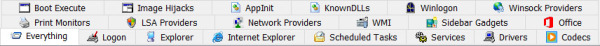
FIGURE 4-8 Autostart categories are displayed on up to 20 different tabs.
Logon
This tab lists the “standard” autostart entries that are processed when Windows starts up and a user logs on, and it includes the ASEPs that are probably the most commonly used by applications. They include the various Run and RunOnce keys in the registry, the Startup directories in the Start menu, computer startup and shutdown scripts, and logon and logoff scripts. It also lists the initial user session processes, such as the Userinit process and the desktop shell. These ASEPs include both per-user and systemwide locations, and entries designed for control through Group Policy. Finally, it lists the Active Setup\Installed Components keys, which although never publicly documented or supported for third-party use have been reverse-engineered and repurposed both for good and for ill.
The following lists the Logon ASEP locations that Autoruns inspects on a particular instance of an x64 version of Windows 10.
The Startup directory in the “all users” Start menu
%ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
The Startup directory in the user’s Start menu
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
Per-user ASEPs under HKCU\Software
HKCU\Software\Microsoft\Windows\CurrentVersion\Run HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce HKCU\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Microsoft\Windows\CurrentVersion\Run HKCU\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Microsoft\Windows\CurrentVersion\Runonce HKCU\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Microsoft\Windows\CurrentVersion\RunonceEx HKCU\Software\Microsoft\Windows NT\CurrentVersion\Windows\Load HKCU\Software\Microsoft\Windows NT\CurrentVersion\Windows\Run HKCU\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Shell
Per-user ASEPs under HKCU\Software—64-bit only
HKCU\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Run HKCU\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\RunOnc
Per-user ASEPs under HKCU\Software intended to be controlled through Group Policy
HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System\Shell HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logon HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff
Systemwide ASEPs in the registry
HKLM\Software\Microsoft\Windows\CurrentVersion\Run HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnceEx HKLM\Software\Microsoft\Active Setup\Installed Components HKLM\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Microsoft\Windows\CurrentVersion\Run HKLM\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Microsoft\Windows\CurrentVersion\Runonce HKLM\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Microsoft\Windows\CurrentVersion\RunonceEx HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\IconServiceLib HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\AlternateShells\AvailableShells HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\AppSetup HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Shell HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Taskman HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\VmApplet HKLM\System\CurrentControlSet\Control\SafeBoot\AlternateShell HKLM\System\CurrentControlSet\Control\Terminal Server\Wds\rdpwd\StartupPrograms HKLM\System\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp\InitialProgram
Systemwide ASEPs in the registry, intended to be controlled through Group Policy
HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System\Shell HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Logon HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Logoff HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown HKLM\Software\Microsoft\Windows\CurrentVersion\Group Policy\Scripts\Startup HKLM\Software\Microsoft\Windows\CurrentVersion\Group Policy\Scripts\Shutdown
Systemwide ASEPs in the registry—64-bit only
HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Run HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\RunOnce HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\RunOnceEx HKLM\Software\Wow6432Node\Microsoft\Active Setup\Installed Components
Systemwide ActiveSync ASEPs in the registry
HKLM\Software\Microsoft\Windows CE Services\AutoStartOnConnect HKLM\Software\Microsoft\Windows CE Services\AutoStartOnDisconnect
Systemwide ActiveSync ASEPs in the registry—64-bit only
HKLM\Software\Wow6432Node\Microsoft\Windows CE Services\AutoStartOnConnect HKLM\Software\Wow6432Node\Microsoft\Windows CE Services\AutoStartOnDisconnect
Explorer
The Explorer tab lists common autostart entries that hook directly into Windows Explorer3 and usually run in-process with Explorer.exe. Again, although most entries are systemwide, there are a number of per-user entries. Key entries on the Explorer tab include the following:
Shell extensions that add context menu items, modify property pages, and control column displays in folder windows
Namespace extensions such as the Desktop, Control Panel, and Recycle Bin, as well as third-party namespace extensions
Pluggable namespace handlers, which handle standard protocols such as http, ftp, and mailto, as well as Microsoft or third-party extensions such as about, mk, and res
Pluggable MIME filters
On 64-bit versions of Windows, in-process components such as DLLs can be loaded only into processes built for the same CPU architecture. For example, shell extensions implemented as 32-bit DLLs can be loaded only into the 32-bit version of Windows Explorer—and 64-bit Windows uses the 64-bit Explorer by default. Therefore, these extensions might not appear to work at all on 64-bit Windows.
The following lists the Explorer ASEP locations that Autoruns inspects on a particular instance of an x64 version of Windows 10.
Per-user ASEPs under HKCU\Software
HKCU\Software\Classes\*\ShellEx\ContextMenuHandlers
HKCU\Software\Classes\*\ShellEx\PropertySheetHandlers
HKCU\Software\Classes\AllFileSystemObjects\ShellEx\ContextMenuHandlers
HKCU\Software\Classes\AllFileSystemObjects\ShellEx\DragDropHandlers
HKCU\Software\Classes\AllFileSystemObjects\ShellEx\PropertySheetHandlers
HKCU\Software\Classes\Clsid\{AB8902B4-09CA-4bb6-B78D-A8F59079A8D5}\Inprocserver32
HKCU\Software\Classes\Directory\Background\ShellEx\ContextMenuHandlers
HKCU\Software\Classes\Directory\ShellEx\ContextMenuHandlers
HKCU\Software\Classes\Directory\Shellex\CopyHookHandlers
HKCU\Software\Classes\Directory\Shellex\DragDropHandlers
HKCU\Software\Classes\Directory\Shellex\PropertySheetHandlers
HKCU\Software\Classes\Drive\ShellEx\ContextMenuHandlers
HKCU\Software\Classes\Folder\Shellex\ColumnHandlers
HKCU\Software\Classes\Folder\ShellEx\ContextMenuHandlers
HKCU\Software\Classes\Folder\ShellEx\DragDropHandlers
HKCU\Software\Classes\Folder\ShellEx\ExtShellFolderViews
HKCU\Software\Classes\Folder\ShellEx\PropertySheetHandlers
HKCU\Software\Classes\Protocols\Filter
HKCU\Software\Classes\Protocols\Handler
HKCU\Software\Microsoft\Ctf\LangBarAddin
HKCU\Software\Microsoft\Internet Explorer\Desktop\Components
HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers
HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellServiceObjects
HKCU\Software\Microsoft\Windows\CurrentVersion\ShellServiceObjectDelayLoad
Systemwide ASEPs in the registry
HKLM\Software\Classes\*\ShellEx\ContextMenuHandlers HKLM\Software\Classes\*\ShellEx\PropertySheetHandlers HKLM\Software\Classes\AllFileSystemObjects\ShellEx\ContextMenuHandlers HKLM\Software\Classes\AllFileSystemObjects\ShellEx\DragDropHandlers HKLM\Software\Classes\AllFileSystemObjects\ShellEx\PropertySheetHandlers HKLM\Software\Classes\Directory\Background\ShellEx\ContextMenuHandlers HKLM\Software\Classes\Directory\ShellEx\ContextMenuHandlers HKLM\Software\Classes\Directory\Shellex\CopyHookHandlers HKLM\Software\Classes\Directory\Shellex\DragDropHandlers HKLM\Software\Classes\Directory\Shellex\PropertySheetHandlers HKLM\Software\Classes\Drive\ShellEx\ContextMenuHandlers HKLM\Software\Classes\Folder\Shellex\ColumnHandlers HKLM\Software\Classes\Folder\ShellEx\ContextMenuHandlers HKLM\Software\Classes\Folder\ShellEx\DragDropHandlers HKLM\Software\Classes\Folder\ShellEx\ExtShellFolderViews HKLM\Software\Classes\Folder\ShellEx\PropertySheetHandlers HKLM\Software\Classes\Protocols\Filter HKLM\Software\Classes\Protocols\Handler
HKLM\Software\Microsoft\Ctf\LangBarAddin HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\SharedTaskScheduler HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellExecuteHooks HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellServiceObjects HKLM\Software\Microsoft\Windows\CurrentVersion\ShellServiceObjectDelayLoad
Systemwide ASEPs in the registry—64-bit only
HKLM\Software\Wow6432Node\Classes\*\ShellEx\ContextMenuHandlers HKLM\Software\Wow6432Node\Classes\*\ShellEx\PropertySheetHandlers HKLM\Software\Wow6432Node\Classes\AllFileSystemObjects\ShellEx\ContextMenuHandlers HKLM\Software\Wow6432Node\Classes\AllFileSystemObjects\ShellEx\DragDropHandlers HKLM\Software\Wow6432Node\Classes\AllFileSystemObjects\ShellEx\PropertySheetHandlers HKLM\Software\Wow6432Node\Classes\Directory\Background\ShellEx\ContextMenuHandlers HKLM\Software\Wow6432Node\Classes\Directory\ShellEx\ContextMenuHandlers HKLM\Software\Wow6432Node\Classes\Directory\Shellex\CopyHookHandlers HKLM\Software\Wow6432Node\Classes\Directory\Shellex\DragDropHandlers HKLM\Software\Wow6432Node\Classes\Directory\Shellex\PropertySheetHandlers HKLM\Software\Wow6432Node\Classes\Drive\ShellEx\ContextMenuHandlers HKLM\Software\Wow6432Node\Classes\Folder\Shellex\ColumnHandlers HKLM\Software\Wow6432Node\Classes\Folder\ShellEx\ContextMenuHandlers HKLM\Software\Wow6432Node\Classes\Folder\ShellEx\DragDropHandlers HKLM\Software\Wow6432Node\Classes\Folder\ShellEx\ExtShellFolderViews HKLM\Software\Wow6432Node\Classes\Folder\ShellEx\PropertySheetHandlers HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Explorer\SharedTaskScheduler HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Explorer\ShellExecuteHooks HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Explorer\ShellServiceObjects HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\ShellServiceObjectDelayLoad
Internet Explorer
Internet Explorer is designed for extensibility, with interfaces specifically exposed to enable Explorer bars such as the Favorites and History bars, toolbars, and custom menu items and toolbar buttons. And Browser Helper Objects (BHOs) enable almost limitless possibilities for extending the capabilities and user experiences for Internet Explorer.
However, because so much of users’ computer time is spent in a browser, and because much of the high-value information that users handle (such as passwords and credit card information) goes through the browser, it has become a primary target of attackers. The same programmatic interfaces that enable integration with third-party document readers and instant messaging have also been used by spyware, adware, and other malicious endeavors.
The following lists the Internet Explorer ASEP locations that Autoruns inspects on a particular instance of an x64 version of Windows 10.
Per-user ASEPs under HKCU\Software
HKCU\Software\Microsoft\Internet Explorer\Explorer Bars HKCU\Software\Microsoft\Internet Explorer\Extensions HKCU\Software\Microsoft\Internet Explorer\UrlSearchHooks
Systemwide ASEPs in the registry
HKLM\Software\Microsoft\Internet Explorer\Explorer Bars HKLM\Software\Microsoft\Internet Explorer\Extensions HKLM\Software\Microsoft\Internet Explorer\Toolbar HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects
Per-user and systemwide ASEPs in the registry—64-bit only
HKCU\Software\Wow6432Node\Microsoft\Internet Explorer\Explorer Bars HKCU\Software\Wow6432Node\Microsoft\Internet Explorer\Extensions HKLM\Software\Wow6432Node\Microsoft\Internet Explorer\Explorer Bars HKLM\Software\Wow6432Node\Microsoft\Internet Explorer\Extensions HKLM\Software\Wow6432Node\Microsoft\Internet Explorer\Toolbar HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects
Scheduled Tasks
The Scheduled Tasks tab displays entries that are configured to be launched by the Windows Task Scheduler. The Task Scheduler allows programs to be launched on a fixed schedule or upon triggering events, such as a user logging on or the computer being idle for a period of time. Commands scheduled with At.exe also appear in the list. The Task Scheduler was greatly enhanced in Windows Vista, so Windows now makes heavy use of it, and the list on the Scheduled Tasks tab will generally be long unless you hide verified Windows entries.
Because tasks can actually be disabled in Windows (unlike Start menu items), clearing the check box next to a scheduled task in Autoruns disables the task rather than copying it to a backup location.4
If you select Jump To Entry from the Entry menu for a scheduled task entry, Autoruns displays the Task Scheduler user interface, but it does not try to navigate to the selected entry.
Services
Windows services run in noninteractive, user-mode processes that can be configured to start independently of any user logging on, and that are controlled through a standard interface with the Service Control Manager. Multiple services can be configured to share a single process. A common example of this can be seen in Svchost.exe (Host Process for Windows Services), which is specifically designed to host multiple services implemented in separate DLLs.
Services are configured in the subkeys of HKLM\System\CurrentControlSet\Services. The Start value within each subkey determines whether and how the service starts.
Autoruns’ Services tab lists services that are not disabled, unless they were disabled by Autoruns (indicated by the presence of an AutorunsDisabled value in the service’s registry key). The content for the Description column comes from the text or the resource identified by the Description value in the configuration key. The image path column displays the path to the service executable; for Svchost services, Autoruns displays the path to the target DLL identified by the ServiceDll value in the service’s key or its Parameters subkey. There are cases for some services in some versions of Windows where administrative rights are required to view the Parameters key; in these cases, Autoruns displays the path to Svchost.exe in the image path column.
Be certain you know what you are doing when disabling or deleting services. Missteps can leave your system with degraded performance, unstable, or unbootable. And again, note that disabling or deleting a service does not stop the service if it is already running.
One malware technique to watch for is a service that looks like it’s supposed to be part of Windows but isn’t, such as a file named svchost.exe in the Windows directory instead of in System32. Another technique is to make legitimate services dependent on a malware service; removing or disabling the service without fixing the dependency can result in an unbootable system. Autoruns’ Jump To Entry feature is handy for verifying whether the service’s configuration in the registry includes a DependOnService value that you can inspect for dependencies before making changes.
Drivers
Like services, drivers are also configured in the subkeys of HKLM\System\CurrentControlSet\Services, as well as in HKLM\Software\Microsoft\Windows NT\CurrentVersion\Font Drivers. Unlike services, drivers run in kernel mode, thus becoming part of the core of the operating system. Most are installed in System32\Drivers and have a .sys file extension. Drivers enable Windows to interact with various types of hardware, including displays, storage, smartcard readers, and human input devices. They are also used to monitor network traffic and file I/O by antivirus software (and by Sysinternals utilities such as Procmon and Procexp!). And, of course, they are also used by malware, particularly rootkits.
As with services, the Drivers tab displays drivers that are not marked as disabled, except those disabled through Autoruns. The Description value comes from the version resource of the driver file, and the image path points to the location of the driver file.
Most blue-screen crashes are caused by an illegal operation performed in kernel mode, and most of those are caused by a bug in a third-party driver. (Less common reasons for blue screens are faulty hardware, the termination of a system-critical process such as Csrss.exe, or an intentional crash triggered through the keyboard driver’s crash functionality, as described in Knowledge Base article 244139: http://support.microsoft.com/kb/244139.)
You can disable or delete a problematic driver with Autoruns. Doing so will usually take effect after a reboot. As with services, be absolutely certain you know what you are doing when disabling or deleting the configuration of drivers. Many are critical to the operating system, and any misconfiguration might prevent Windows from working at all.
Codecs
The Codecs category lists executable code that can be loaded by media playback applications. Buggy or misconfigured codecs have been known to cause system slowdowns and other problems, and these ASEPs have also been abused by malware. The following lists the keys that are shown on the Codecs tab.
Keys inspected under both HKLM and HKCU
\Software\Classes\CLSID\{083863F1-70DE-11d0-BD40-00A0C911CE86}\Instance
\Software\Classes\CLSID\{7ED96837-96F0-4812-B211-F13C24117ED3}\Instance
\Software\Classes\CLSID\{ABE3B9A4-257D-4B97-BD1A-294AF496222E}\Instance
\Software\Classes\CLSID\{AC757296-3522-4E11-9862-C17BE5A1767E}\Instance
\Software\Classes\Filter
\Software\Microsoft\Windows NT\CurrentVersion\Drivers32
Keys inspected under both HKLM and HKCU on 64-bit Windows
\Software\Wow6432Node\Classes\CLSID\{083863F1-70DE-11d0-BD40-00A0C911CE86}\Instance
\Software\Wow6432Node\Classes\CLSID\{7ED96837-96F0-4812-B211-F13C24117ED3}\Instance
\Software\Wow6432Node\Classes\CLSID\{ABE3B9A4-257D-4B97-BD1A-294AF496222E}\Instance
\Software\Wow6432Node\Classes\CLSID\{AC757296-3522-4E11-9862-C17BE5A1767E}\Instance
\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32
Boot Execute
The Boot Execute tab shows you Windows native-mode executables that are started by the Session Manager (Smss.exe) during system boot. BootExecute typically includes tasks, such as hard-drive verification and repair (Autochk.exe), that cannot be performed while Windows is running. The Execute, S0InitialCommand, and SetupExecute entries should never be populated after Windows has been installed. The following lists the keys that are displayed on the Boot Execute tab.
Keys that are displayed on the Boot Execute tab
HKLM\System\CurrentControlSet\Control\ServiceControlManagerExtension HKLM\System\CurrentControlSet\Control\Session Manager\BootExecute HKLM\System\CurrentControlSet\Control\Session Manager\Execute HKLM\System\CurrentControlSet\Control\Session Manager\S0InitialCommand HKLM\System\CurrentControlSet\Control\Session Manager\SetupExecute
Image hijacks
Image hijacks is the term I use for ASEPs that run a different program from the one you specify and expect to be running. The Image Hijacks tab displays four types of these redirections:
exefile Changes to the association of the .exe or .cmd file types with an executable command. The file-association user interfaces in Windows have never exposed a way to change the association of the .exe or .cmd file types, but they can be changed in the registry. Note that there are per-user and systemwide versions of these ASEPs.
htmlfile Changes to the association of the .htm or .html file types with an executable command. Some malware that hijacks these ASEPs can come into play when you open an HTML file. Verify that the executable command is a legitimate browser.
Command Processor\Autorun A command line that is executed whenever a new Cmd.exe instance is launched. The command runs within the context of the new Cmd.exe instance. There is a per-user and systemwide variant, as well as a separate version for the 32-bit Cmd.exe on 64-bit Windows.
Image File Execution Options (IFEO) Subkeys of this registry location (and its echo in the 64-bit versions of Windows) are used for a number of internal and undocumented purposes. One purpose for IFEO subkeys that has been documented is the ability to specify an alternate program to start whenever a particular application is launched. By creating a subkey named for the file name of the original program and a “Debugger” value within that key that specifies an executable path to an alternate program, the alternate program is started instead and receives the original program path and command line on its command line. The original purpose of this mechanism was for the alternate program to be a debugger and for the new process to be started by that debugger, rather than having a debugger attach to the process later, after its startup code had already run. However, there is no requirement that the alternate program actually be a debugger, nor that it even look at the command line passed to it. In fact, this mechanism is how Process Explorer (described in Chapter 3) replaces Task Manager.
The following list shows the registry keys corresponding to these ASEPS that are shown on the Image Hijacks tab.
Registry locations inspected for EXE file hijacks
HKCU\Software\Classes\Exefile\Shell\Open\Command\(Default) HKCU\Software\Classes\.exe HKCU\Software\Classes\.cmd HKLM\Software\Classes\Exefile\Shell\Open\Command\(Default) HKLM\Software\Classes\.exe HKLM\Software\Classes\.cmd
Registry locations inspected for htmlfile hijacks
HKCU\Software\Classes\Htmlfile\Shell\Open\Command\(Default) HKLM\Software\Classes\Htmlfile\Shell\Open\Command\(Default)
Command processor autorun keys
HKCU\Software\Microsoft\Command Processor\Autorun HKLM\Software\Microsoft\Command Processor\Autorun HKLM\Software\Wow6432Node\Microsoft\Command Processor\Autorun
Keys inspected for Image File Execution Options hijacks
HKLM\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Image File Execution Options
AppInit
The idea behind AppInit DLLs surely seemed like a good idea to the software engineers who incorporated it into Windows NT 3.1. Specify one or more DLLs in the Appinit_Dlls registry key, and those DLLs will be loaded into every process that loads User32.dll (that is, virtually all user-mode Windows processes). Well, what could go wrong with that?
The AppInit DLLs are loaded into the process during User32’s initialization—that is, while its DllMain function is executing. Developers are explicitly told not to load other DLLs within a DllMain. It can lead to deadlocks and out-of-order loads, which can lead to application crashes. And yet here, the AppInit DLL “feature” does exactly that. And yes, that has led to deadlock and application crashes.5
A DLL that automatically gets loaded into every process on the computer sounds like a winner if you are writing malware. Although AppInit has been used in legitimate (but misguided) software, it is frequently used by malware.
Because of these problems, AppInit DLLs are deprecated and disabled by default in Windows Vista and newer. For purposes of backward compatibility, it is possible to re-enable AppInit DLL functionality, but doing so is strongly discouraged. To ensure that AppInit DLLs have not been re-enabled, verify that the LoadAppInit_DLLs DWORD value is 0 in HKLM\Software\Microsoft\Windows NT\CurrentVersion\Windows and in HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Windows.
Registry values inspected for AppInit Entries
HKLM\Software\Microsoft\Windows NT\CurrentVersion\Windows\Appinit_Dlls HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Windows\Appinit_Dlls HKLM\System\CurrentControlSet\Control\Session Manager\AppCertDlls
KnownDLLs
KnownDLLs helps improve system performance by ensuring that all Windows processes use the same version of certain DLLs, rather than choose their own from various file locations. During startup, the Session Manager maps the DLLs listed in HKLM\System\CurrentControlSet\Control\Session Manager\KnownDlls into memory as named section objects. When a new process is loaded and needs to map these DLLs, it uses the existing sections rather than searching the file system for another version of the DLL.
The Autoruns KnownDLLs tab should contain only verifiable Windows DLLs. On 64-bit versions of Windows, the KnownDLLs tab lists one ASEP, but file entries are duplicated for both 32-bit and 64-bit versions of the DLLs, in directories specified by the DllDirectory and DllDirectory32 values in the registry key. Note that the Windows-On-Windows-64 (WOW64) support DLLs are present only in the System32 directory and Autoruns will report “file not found” for the corresponding SysWOW64 directory entries. This is normal.
To verify that malware hasn’t deleted an entry from this key so that it can load its own version of a system DLL, save the Autoruns results from the suspect system and compare it against the results from a known-good instance of the same operating system. See the “Saving and comparing results” section later in this chapter for more information.
Winlogon
The Winlogon tab displays entries that hook into Winlogon.exe, which manages the Windows interactive-logon user interface. Introduced in Windows Vista, the Credential Provider interface manages the user authentication interface. Today, Windows includes many credential providers that handle password, PIN, picture-password, smartcard, and biometric logon. Most of these are shown only if you disable the Hide Windows Entry option. Third parties can supply credential providers that further customize interactive user logons.
The Winlogon tab also includes the user’s configured screen saver, which is started by Winlogon.exe after inactivity, and registered Group Policy client-side extensions (CSEs), which are DLLs that the Group Policy engine loads. The Group Policy engine used to run in the Winlogon process, but now it runs in the Group Policy Client service.
The following list specifies the registry keys that are shown on the Winlogon tab.
Per-user specification of the screen saver
HKCU\Control Panel\Desktop\Scrnsave.exe
Per-user specification of the screen saver, controlled by Group Policy
HKCU\Software\Policies\Microsoft\Windows\Control Panel\Desktop\Scrnsave.exe
Group Policy Client-Side Extensions (CSEs)
HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\GPExtensions HKLM\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Winlogon\GPExtensions
Credential provider ASEPs
HKLM\Software\Microsoft\Windows\CurrentVersion\Authentication\Credential Provider Filters HKLM\Software\Microsoft\Windows\CurrentVersion\Authentication\Credential Providers HKLM\Software\Microsoft\Windows\CurrentVersion\Authentication\PLAP Providers
Systemwide identification of a program to verify successful boot
HKLM\System\CurrentControlSet\Control\BootVerificationProgram\ImagePath
ASEP for custom setup and deployment tasks
HKLM\System\Setup\CmdLine
Winsock providers
Windows Sockets (Winsock) is an extensible API on Windows because third parties can add a transport service provider that interfaces Winsock with other protocols or layers on top of existing protocols to provide functionality such as proxying. Third parties can also add a namespace service provider to augment Winsock’s name-resolution facilities. Service providers plug into Winsock by using the Winsock service provider interface (SPI). When a transport service provider is registered with Winsock, Winsock uses the transport service provider to implement socket functions, such as connect and accept, for the address types that the provider indicates it implements. There are no restrictions on how the transport service provider implements the functions, but the implementation usually involves communicating with a transport driver in kernel mode.
The Winsock tab lists the providers registered on the system, including those that are built into Windows. You can hide the latter group by enabling Hide Windows Entries and Verify Code Signatures to focus on the entries that are more likely to be causing problems.
Keys inspected for Winsock Provider Entries
HKLM\System\CurrentControlSet\Services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries HKLM\System\CurrentControlSet\Services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries64 HKLM\System\CurrentControlSet\Services\WinSock2\Parameters\Protocol_Catalog9\Catalog_Entries HKLM\System\CurrentControlSet\Services\WinSock2\Parameters\Protocol_Catalog9\Catalog_Entries64
Print monitors
The entries listed on the Print Monitors tab are DLLs that are configured in the subkeys of HKLM\System\CurrentControlSet\Control\Print\Monitors. These DLLs are loaded into the Spooler service, which runs as Local System.
LSA providers
This category of autostarts comprises packages that define or extend user authentication for Windows, via the Local Security Authority (LSA). Unless you have installed third-party authentication packages or password filters, this list should contain only Windows-verifiable entries. The DLLs listed in these entries are loaded by Lsass.exe or Winlogon.exe and run as Local System.
The SecurityProviders ASEP that is also shown on this tab lists registered cryptographic providers. DLLs listed in this ASEP get loaded into many privileged and standard user processes, so this ASEP has been targeted as a malware persistence vector. (This ASEP isn’t truly related to the LSA, except that, like the LSA, it represents security-related functionality.)
Keys inspected for Authentication Providers
HKLM\System\CurrentControlSet\Control\Lsa\Authentication Packages HKLM\System\CurrentControlSet\Control\Lsa\Notification Packages HKLM\System\CurrentControlSet\Control\Lsa\Security Packages HKLM\System\CurrentControlSet\Control\Lsa\OSConfig\Security Packages
Keys inspected for Registered Cryptographic Providers
HKLM\System\CurrentControlSet\Control\SecurityProviders\SecurityProviders
Network providers
The Network Providers tab lists the installed providers handling network communication, which are configured in HKLM\System\CurrentControlSet\Control\NetworkProvider\Order. On a Windows desktop operating system, for example, this tab includes the default providers that provide access to SMB (file and print) servers, Microsoft RDP (Terminal Services/Remote Desktop) servers, and access to WebDAV servers. Additional providers are often visible in this list if you have a more heterogeneous network or additional types of servers that Windows needs to connect to. All entries in this list should be verifiable.
WMI
The WMI tab lists registered WMI event consumers that can be configured to run arbitrary scripts or command lines when a particular event occurs. When you select an entry on the WMI tab, the lower panel reports information about the target file, the event consumer’s full command line, and the condition, such as a WQL query, that will trigger the event consumer to execute.
When you disable a WMI entry, Autoruns replaces the entry with a clone that has the same name but with “_disabled” appended. This breaks the binding to the event filter so that it won’t execute. By re-enabling, the original name and the event binding is reestablished.
These events and bindings are stored in the WMI repository in the ROOT\subscription namespace.
Sidebar gadgets
On Windows Vista and Windows 7, this tab lists the Sidebar Gadgets (called “Desktop Gadgets” on Windows 7) that are configured to appear on the user’s desktop. Although gadget software is often (but not always) installed in a systemwide location such as %ProgramFiles%, the configuration of which gadgets to run is in %LOCALAPPDATA%\Microsoft\Windows Sidebar\Settings.ini, which is per-user and nonroaming. Disabling or deleting gadgets with Autoruns manipulates entries in the Settings.ini file.
The image path usually points to an XML file. The gadgets that shipped with Windows Vista and Windows 7 are catalog signed and can be verified. Gadgets were discontinued after Windows 7.
Office
The Office tab lists add-ins and plug-ins registered to hook into documented interfaces for Access, Excel, Outlook, PowerPoint, and Word. On 64-bit Windows, Office add-ins can be registered to run in 32-bit or 64-bit Office versions. 32-bit add-ins are registered in Wow6432Node subkeys on 64-bit Windows.
Keys inspected under both HKLM and HKCU
\Software\Microsoft\Office\Access\Addins \Software\Microsoft\Office\Excel\Addins \Software\Microsoft\Office\Outlook\Addins \Software\Microsoft\Office\PowerPoint\Addins \Software\Microsoft\Office\Word\Addins
Keys inspected under both HKLM and HKCU on 64-bit Windows
\Software\Wow6432Node\Microsoft\Office\Access\Addins \Software\Wow6432Node\Microsoft\Office\Excel\Addins \Software\Wow6432Node\Microsoft\Office\Outlook\Addins \Software\Wow6432Node\Microsoft\Office\PowerPoint\Addins \Software\Wow6432Node\Microsoft\Office\Word\Addins

 Note
Note